This blog originally appeared in April 2021 on the Area 1 Security website, and was issued in advance of Cloudflare's acquisition of Area 1 Security on April 1, 2022. Learn more.
AMERICA! WE HAVE A 2021 MARCH HACKNESS CHAMPION! (Granted, it’s a phishy title that no organization really wants to win).
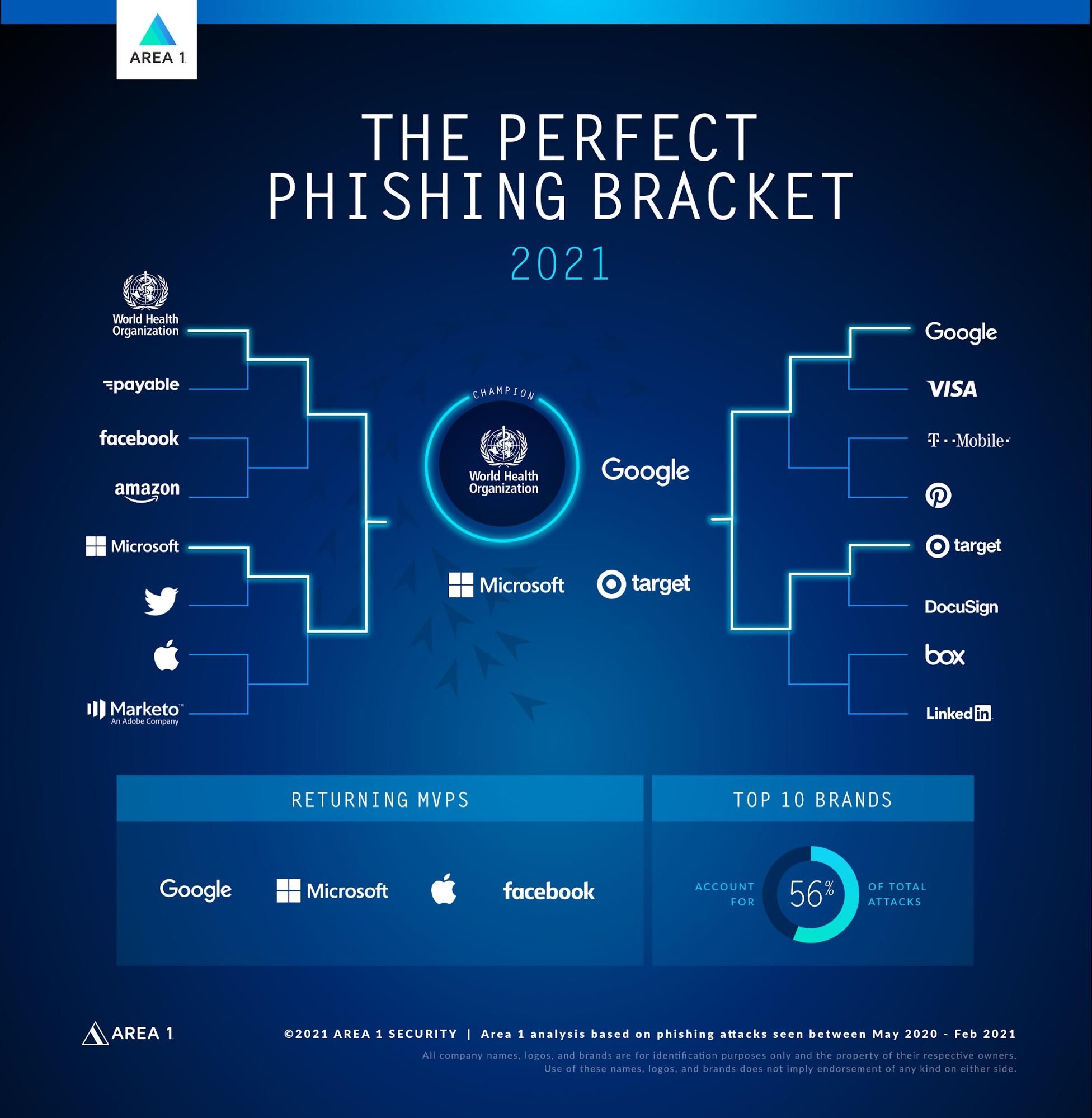
A Cinderella story. The underdog. The New Kid on the Block is … the World Health Organization!
Although the WHO won’t want you to get fooled (with phishing) again, they are the undisputed March Hackness Champion of 2021!
Truly, what a difference a year makes. The COVID-19 pandemic changed the world, including the world of Phishing and cyberattack lures. Our researchers identified over 2 million Phishing spoofs (out of more than 22 million) that specifically exploited the WHO brand between May 2020 to February 2021.
For example, in this phishing message from last year, the attacker lures victims by posing as the WHO, claiming to offer safety measures on how to stop the spread of the virus. We see Display Name Spoofing, where the true sender is actually this alansariornan[.]com domain.
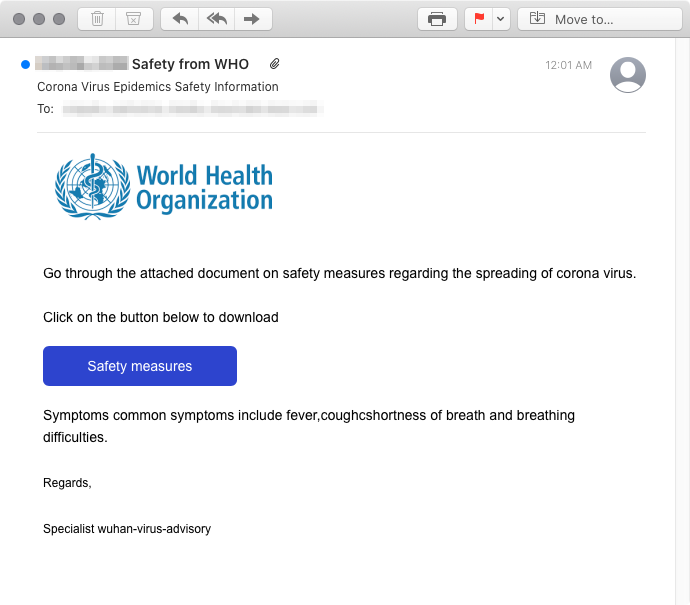
In an attempt to add legitimacy to the phishing example above:
- The attacker added the logo for the WHO in the body of their message. This is a common tactic, which Area 1 uses to help detect malicious messages (more specifically, our advanced computer vision algorithms and statistical models essentially train computers to interpret and understand digital images).
- The attacker also used a fairly sophisticated technique to avoid detection by abusing the legitimate service, Appspot.com, to host their phishing site. Appspot is a cloud computing platform for developing and hosting web apps in Google-managed data centers, so naturally, those domains are commonly whitelisted — and the corresponding links are not typically evaluated.
- Campaigns like this use well-designed login pages in an attempt to capture login credentials, which are then sent to a remote server controlled by the attacker.
Attackers cleverly and maliciously pivoted to exploit other COVID-19 trends, such as businesses sending more sales emails, consumers shopping online more, the real estate surge, and the growth of online news content consumption.
Aside from the likes of the WHO (#1), Moderna (#25) and CDC (#48), these companies (whether they like it or not!) also made our annual phishing bracket for the first time this year:
- #7 — Marketo
- #20 — Columbia Sportswear
- #24 — UPS
- #38 — CNN
- #50 — Zoom
- #51 — Adidas
- #53 — Nike
- #63 — Zillow
Much like in the real tournament, there were several upsets in the Phishing brackets as well. Former 2017 and 2019 March Hackness bracket champion, PayPal, didn’t even crack the Sweet 16 round this time.
With the world on edge in 2020, hackers took every advantage they could to find a way into organizations. Their weapon of choice is trust. Who wouldn’t want information from the WHO about a virus that is affecting every aspect of their lives? Hackers know this, so they use it.
And as I shared in our prior Not-so-Sweet 16 post, email authentication and sender reputation standards (such as SPF, DKIM and DMARC) aren’t enough to prevent phishing attacks from reaching inboxes.
Email authentication and sender reputation were designed to help brands deliver their email messages properly — not to help defend your organization from the most sophisticated phish.
In fact, our co-founder/CSO, Blake Darché, and our principal security researcher, Javier Castro, demonstrated through the creation of a real-time, DMARC-passing attack, just how fast and easy it is for attackers to get phishing emails into your inbox.
Remember, even when you deploy DMARC for your domain:
- It’s easy it is to establish a new phishing domain that exploits trusted infrastructure
- It’s fast to set up DMARC, SPF and DKIM policies for new phishing domains in order to reach inboxes
- You need to detect phish beyond email authentication via comprehensive message analysis, computer vision, domain registration checks, and other techniques beyond email authentication.
Takeaways from the 2021 March Hackness Tournament
Here are some other key insights on the past year’s contenders:
- The Top 4 “seeds” were seen in over 6 million phishing attacks.
- The Top 10 accounted for over 56% of ALL spoof- and impersonation-based phishing attacks.
- Our 64-brand bracket included 15 different industries. The most well-represented were Technology and Financial Services/Banking.
- Attackers will use what is in the headlines to make attacks land. COVID-19 and a Presidential Election heavily influenced the attack patterns of phishing attacks in the U.S. last year.
Well America, I had a great time with you for the 2021 March Hackness tournament. Will our Cinderella return to the ball next year? You’ll have to join us again to find out!
Until next time… (Dick Vitale one last time)
GOODNIGHT BABY! WE’LL BE DANCING AGAIN NEXT YEAR!